A ZTNA (Zero Trust Network Access) architecture is not a “plug-and-play” product, but a set of interconnected best practices designed to ensure granular and secure access. The core of the model lies in continuous authentication and authorization: every single request is dynamically verified based on identity (via MFA or biometrics) and device health.
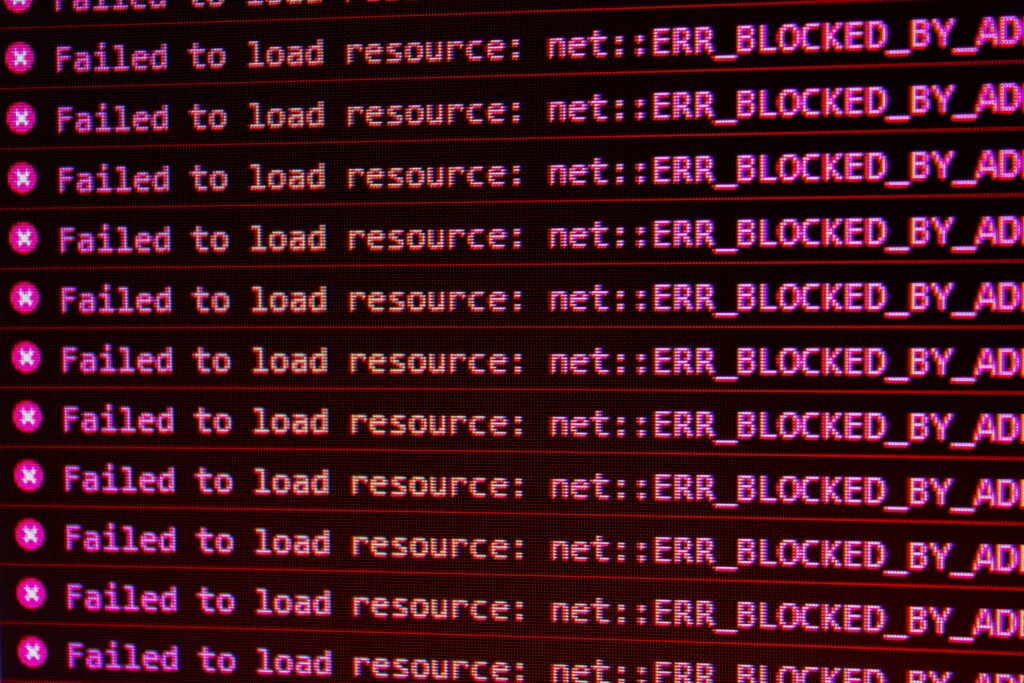
This approach eliminates network visibility for the user by implementing application-level segmentation. The result? A drastically reduced attack surface and the strict limitation of lateral movement in the event of a breach.
To implement these strategies without compromising business performance, it is essential to rely on managed cybersecurity services capable of orchestrating advanced policy engines in real-time.
Operational criticalities: where does complexity hide?
Moving from theory to practice reveals significant obstacles. Managing federated identities across SaaS systems, on-premises infrastructures, and OT environments highlights the limits that Zero Trust doctrine does not solve by default.
There is a natural friction between security (based on rigid RBAC/ABAC rules) and the business, which demands fluidity and collaboration with external partners. When rules become too complex, users seek shortcuts, fueling Shadow IT and a bypass of security protocols.
Furthermore, the legacy world represents a massive challenge: micro-segmenting outdated VMs or non-standardized hardware often creates gaps between declared orchestration and actual enforcement. In this context, solid governance and risk management is the only way to balance operational agility with the necessary technical rigor.
Zero Trust maturity model: measuring progress
To navigate this transition, the most authoritative reference is the CISA Zero Trust Maturity Model (ZTMM) , which defines an evolutionary path across a maturity scale: Traditional, Initial, Advanced, and Optimal.
The model is built upon five fundamental pillars:
- Identity: Lifecycle management and least-privilege access.
- Devices: Continuous compliance and device posture isolation.
- Networks: Micro-segmentation and East-West traffic control.
- Applications & Workloads: Contextual access and API protection.
- Data: Dynamic classification and encryption in-use.
The future of ZTNA: AI and adaptive security
The evolutionary directions are now clear. In the near future, we will witness:
- Adaptive policies: Powered by AI to update in real-time based on detected anomalous behavior (UEBA).
- Confidential computing: To extend Zero Trust directly into data during the processing phase.
- VPN replacement: Adaptive Security will become the standard response for mobile users and IoT devices, overcoming the limits of static segmentation.
The journey toward Zero Trust cannot be improvised. It requires a clear roadmap that integrates technology with corporate culture, transforming security into a true engine of resilience.
Raffaele Sarno
Head Pre-sale Manager, NEVERHACK Security Operation Department, Italy